The Threat Stream API endpoint is located at https://api.threatstream.com/api/v1/. You can find the Threat Stream API portal / hompage here. The Threat Stream API is not currently available on the RapidAPI marketplace.
Click "Request this API on RapidAPI" to let us know if you would like to access to this API.
Meanwhile, you can check out the top APIs that currently available for developers.
Related Articles
Related Threat Stream API Articles
![DDoS threat report for 2024 Q1 - RapidAPI]()
DDoS threat report for 2024 Q12024 started with a bang. Cloudflare’s autonomous systems mitigated over 4.5 million DDoS attacks in the first quarter of the year — a 50% increase compared to the previous year. Read the full coverage:
Node v20.12.0 (LTS)Node.js® is a JavaScript runtime built on Chrome's V8 JavaScript engine.
![AI-powered SQL Query Converter Tool is Now Available in Relational Migrator - RapidAPI]()
AI-powered SQL Query Converter Tool is Now Available in Relational MigratorWhen I traveled to Japan for the first time it was shortly after translation apps on smartphones had really taken off. Even though I knew enough phrases to get by as a tourist I was amazed at how empowered I was by being able to have smoother conversations an…
![Architecting Success as a Woman in Tech - RapidAPI]()
Architecting Success as a Woman in TechCelia Halenke, Solutions Architect at MongoDB, shares insight into the skills, experiences, and aspirations that shape her MongoDB journey in the dynamic world of technology. Plus, learn about her advice for teams wanting to build more inclusive environments …
![Major data center power failure (again): Cloudflare Code Orange tested - RapidAPI]()
Major data center power failure (again): Cloudflare Code Orange testedJust four months after a complete power outage at a critical data center we were hit with the exact same scenario. Here’s how we did this time, and what’s next.
![Four generative AI cyber risks that keep CISOs up at night — and how to combat them - RapidAPI]()
Four generative AI cyber risks that keep CISOs up at night — and how to combat themIn this episode of the SecurityANGLE, host Shelly Kramer, managing director and principal analyst at theCUBE Research, is joined by analyst, engineer and theCUBE Collective community member Jo Peterson for a conversation about the top four generative artifici…
![Prompt Engineering And The Newly Released Prompt Shields And Spotlight Prompting Techniques Are Useful For Protecting Your Generative AI From Baddies And Even Yourself - RapidAPI]()
Prompt Engineering And The Newly Released Prompt Shields And Spotlight Prompting Techniques Are Useful For Protecting Your Generative AI From Baddies And Even YourselfThe latest in prompt engineering for generative AI is the emergence of prompt shields and spotlighting prompting techniques. Here's what you need to know.
![RapidAPI logo]()
A peek at CSS Anchor positioning
#639 — April 17, 2024 | Read on the webFrontend Focus
E2EE enhanced patient-centric blockchain-based system for EHR managementTo secure sensitive medical records in the healthcare clouds, this paper proposes an End-to-End Encryption (E2EE) to enhance a patient-centric blockchain-based system for electronic health record (EHR) management. The suggested system with a focus on the pati…
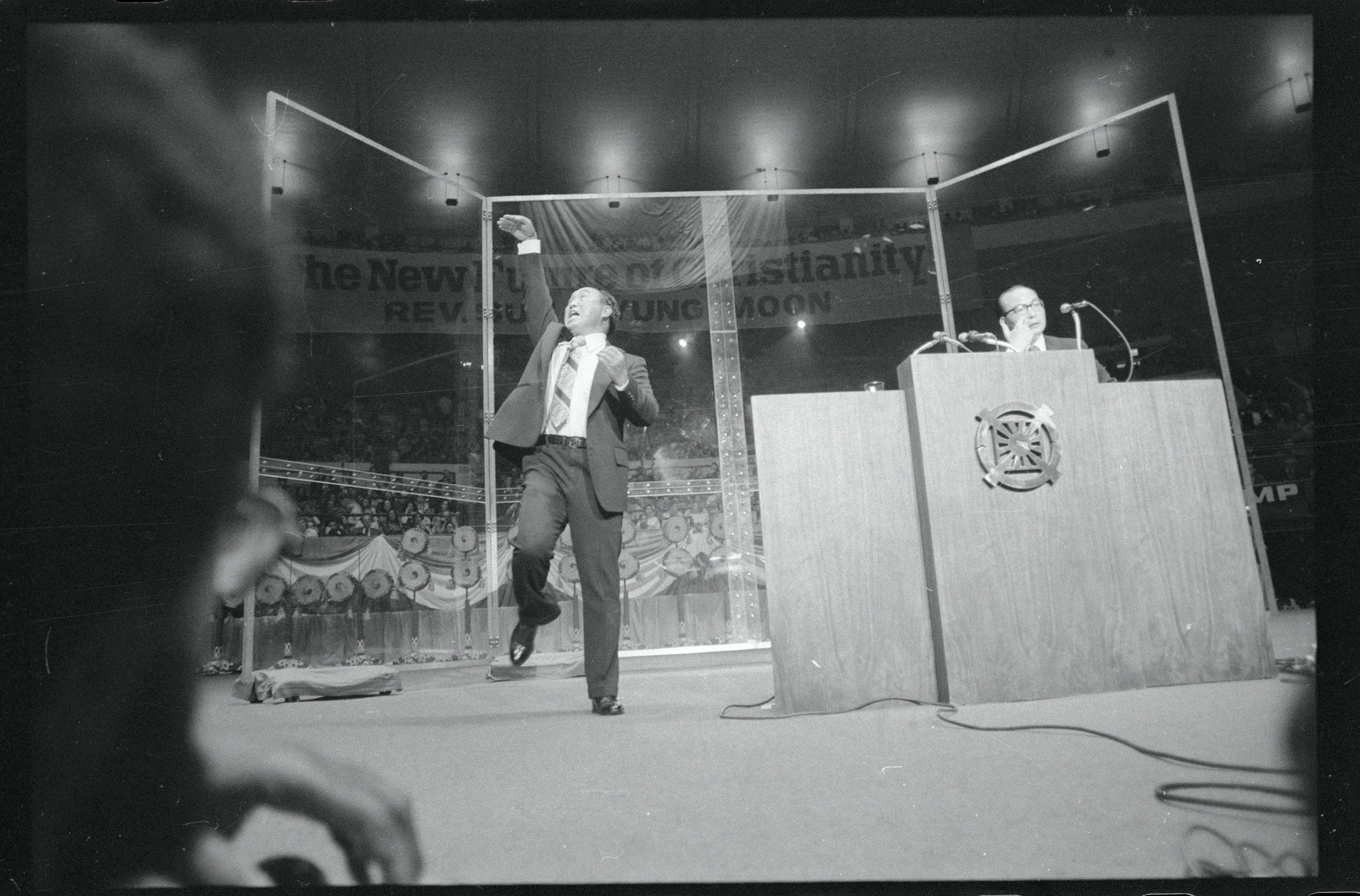
![The Unification Church Infiltrated Japan’s Government. Now Its Sights Are Set on the U.S. - RapidAPI]()
The Unification Church Infiltrated Japan’s Government. Now Its Sights Are Set on the U.S.Following the assassination of Shinzo Abe, the Unification Church is pivoting its fundraising efforts to the U.S. ahead of the election.
![RapidAPI logo]()
Vulnerability Summary for the Week of March 25, 2024High Vulnerabilities
PrimaryVendor -- Product Description Published CVSS Score Source & Patch Info acowebs -- pdf_invoices_and_packing_slips_for_woocommerce Deserial… ![RapidAPI logo]()
Vulnerability Summary for the Week of April 15, 2024High Vulnerabilities
PrimaryVendor -- Product Description Published CVSS Score Source & Patch Info 10web -- slider_by_10web Improper Neutralization of Input During Web … Source: NewsAPI
Related Threat Stream API Videos

administrator

-u4r2d3c4lk.jpg)
-z5cce5ouy9.jpg)